Authorizations
OAuth 2.0
Integray allows you to add new authorizations using the OAuth 2.0 protocol, which stands for “Open Authorization”, a standard designed to allow a website or application to access resources hosted by other web apps on behalf of a user. It replaced OAuth 1.0 in 2012 and is now the de facto industry standard for online authorization. OAuth 2.0 provides consented access and restricts actions of what the client app can perform on resources on behalf of the user, without ever sharing the user's credentials.
With Integray, you can select predefined providers or set up custom authorizations using the OAuth 2.0 protocol. It enables you to define and manage scopes, which specify the permissions your application needs. Integray simplifies the process of adding and managing connectors, ensuring that your applications can securely access the necessary resources and services.
Benefits of OAuth 2.0
OAuth 2.0 offers several advantages:
-
Enhanced security: Minimizes the risk of exposing credentials by using authorization tokens.
-
User convenience: Allows you to grant and revoke access to applications without sharing passwords.
-
Scalability: Supports a wide range of applications, including web, mobile, and desktop applications.
Authorizations list
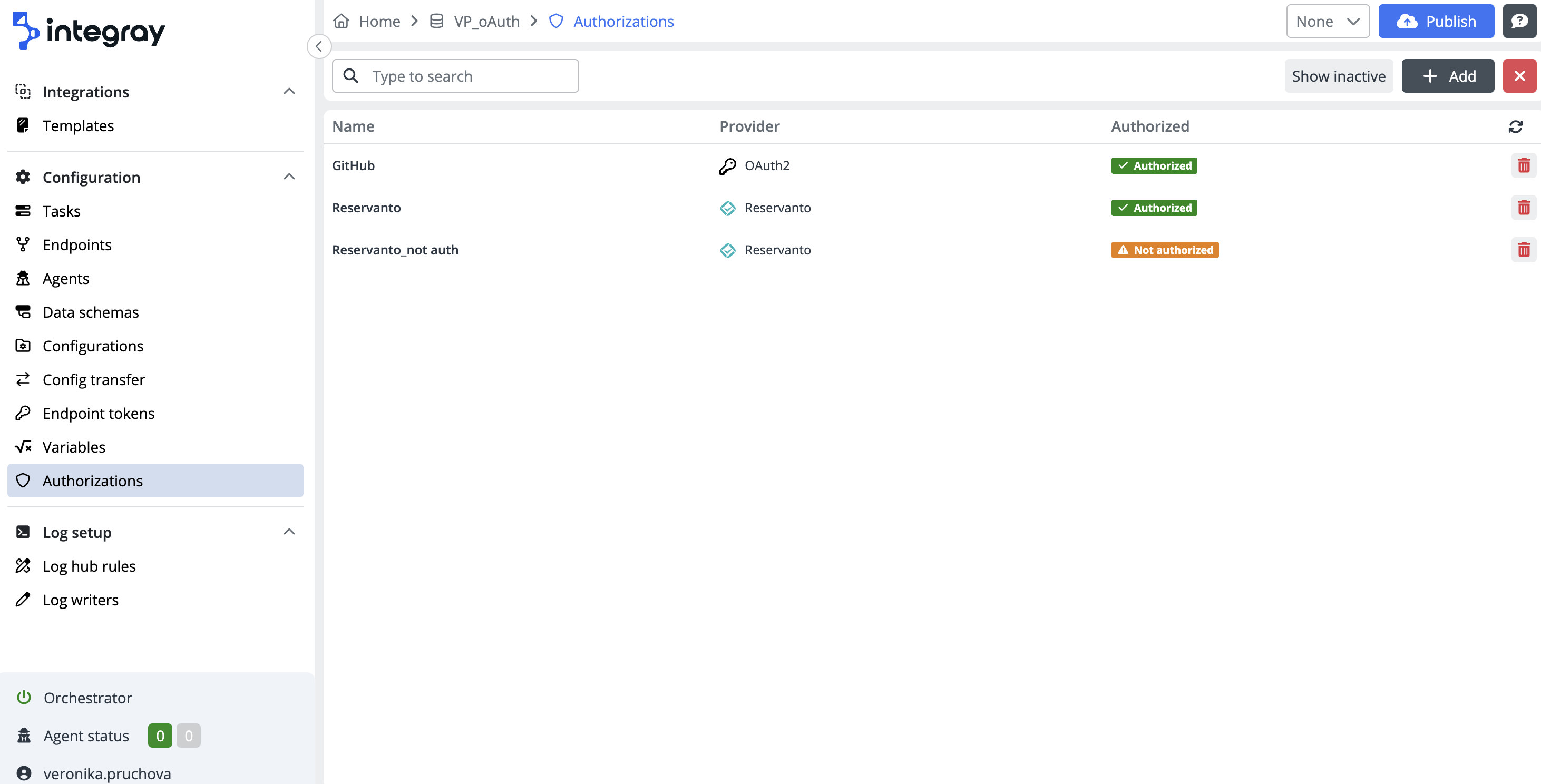
The content navigation menu item Authorizations takes you to the Authorization list, which provides a comprehensive overview and management capabilities for each authorization.
In the upper section of the list interface, you will find a user-friendly search field, enabling you to locate specific authorization quickly.
On the right side of the screen, you can see the Show in/active button, which switches between active and inactive authorization views, and the + Add button, which starts the configuration of a new authorization and opens the editor.
The authorization list view provides you with essential information about the following:
-
Name: The name given to the authorization.
-
Provider: The service provider associated with the authorization. We support two types of providers:
-
Generic: Allows you to configure everything manually according to your specific needs - more information here
-
Predefined: Includes providers like Reservanto or Azure DevOps, which offer predefined settings to simplify and accelerate the configuration process.
-
-
Authorized status: Displays the current status of the authorization, which can be either Not authorized or Authorized.
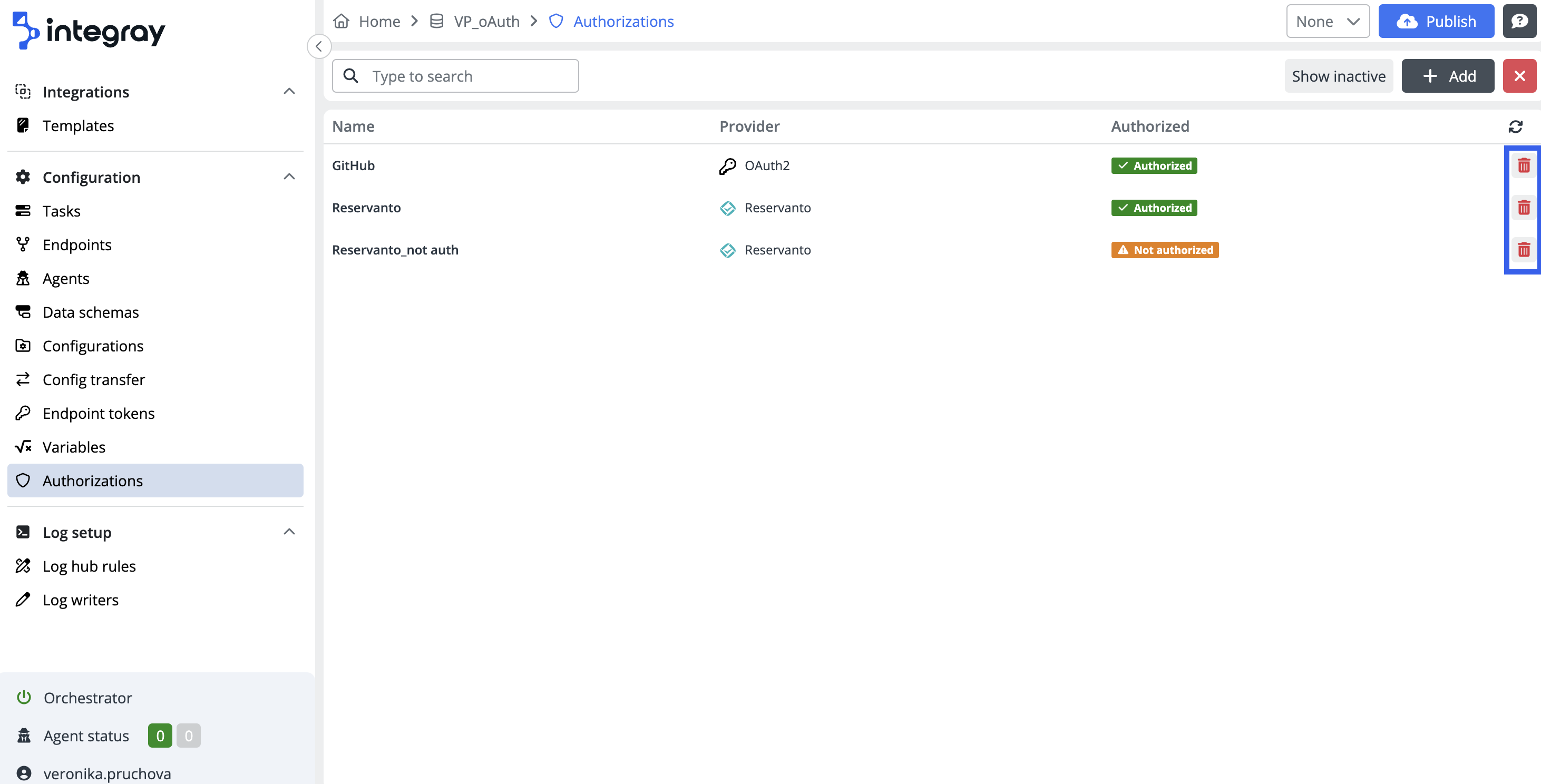
Additionally, each row in the list includes a Deactivate button, which allows you to deactivate the authorization when necessary.
Create authorization
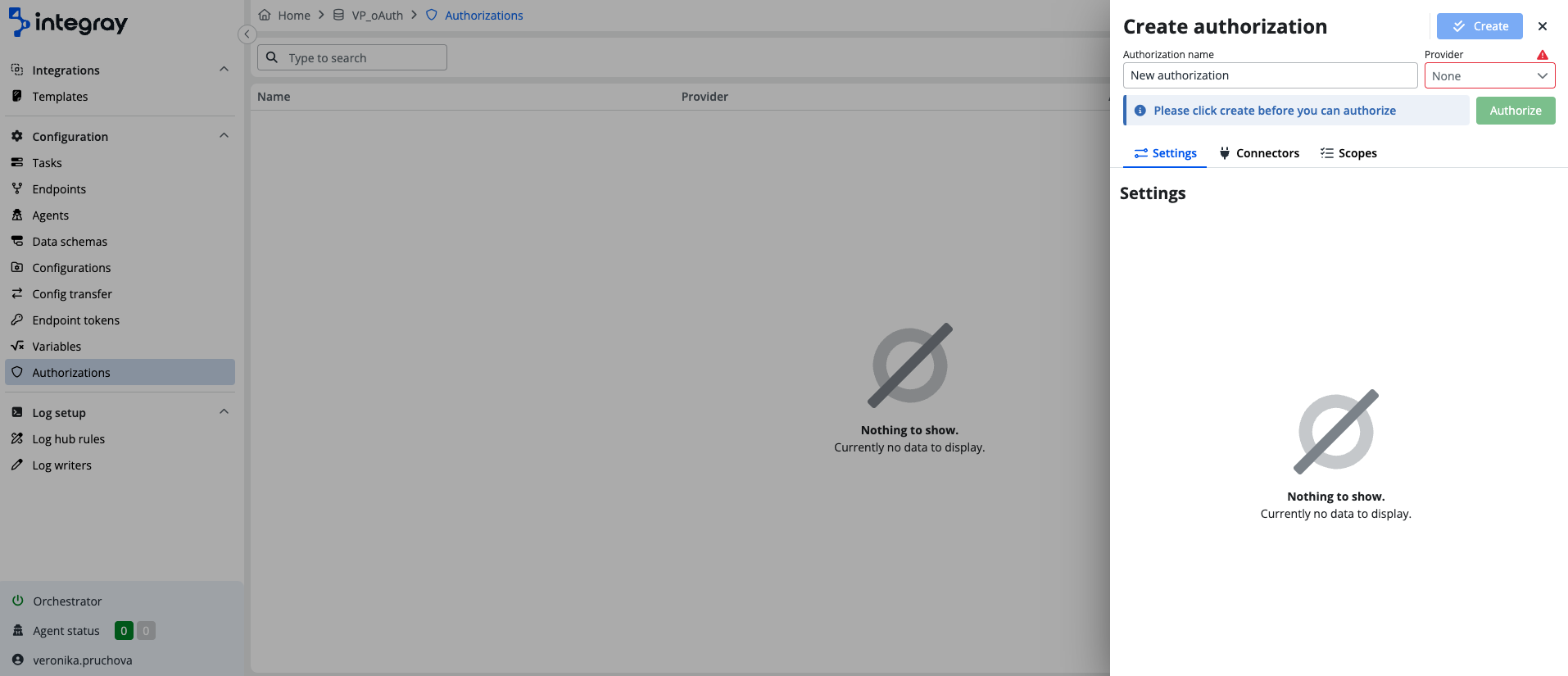
To add a new authorization, navigate to the Authorization list and start by clicking the +Add button. This action opens a form.
Enter the necessary information for the new authorization. Provide a Name for the authorization and select the service Provider from the dropdown list. As mentioned earlier, you can choose between Generic or Predefined providers such as Reservanto or Azure DevOps.
Scopes
Scopes are permission settings that dictate what actions the connector is allowed to perform. The Scopes section section lists the specific permissions for the selected authorization. Each scope defines a particular level of access that the connector needs to perform its tasks with the given service. These scopes ensure that the application only has the permissions necessary to complete its functions.
There are two types of scopes:
Custom scopes
Custom scopes are those that you, as a user, can create to meet specific access requirements necessary for the proper functioning of the authorization. Custom scopes provide the flexibility to define additional or more restrictive permissions, allowing you to tailor the access level precisely according to the needs of your application. This customization ensures that the application operates within the bounds of required permissions, enhancing security and functionality.
Automatic scopes
Automatic scopes are predefined by Integray and are associated with the selected connector or connectors for which the authorization is being created. They are automatically added based on the selected service, ensuring that the connector has the necessary permissions for standard operations. These scopes are designed to cover typical use cases and facilitate a seamless setup process.
For instance (when using Reservanto connectors):
-
Booking_w: This scope might allow the connector to write booking data.
-
Merchant_r: This scope might grant read access to merchant information.
Reauthentication required
You need to reauthenticate with each change. If you modify the scopes or connectors in an existing authorization, you must reauthorize it for the changes to take effect.